Just like that, #wfh became a permanent situation. Rocking business-as-usual, this initial disruption has evolved into something pretty powerful. Reduced overhead costs, increased flexibility (and employee satisfaction) and streamlined operations are all possible with remote teams.
But virtual work is a double-edged sword, something that was made plain from the first days of the COVID-19 pandemic. The reality is, many businesses were unprepared to handle the technology considerations. When 70% or more of your staff is logging into work networks from home computers, a ton of problems can happen.
Let’s dive into some of what those are and what the best companies are doing to provide business computers, business laptops or business tablets, implement high levels of cybersecurity and, ultimately, protect data and end users alike.
BYOD vs COD: Pros & Cons
The major provision required to facilitate remote work is the hardware.
Most businesses faced this decision: make a massive investment in corporate owned devices (COD) like laptops, tablets, webcams, etc. OR let employees “bring your own device” (BYOD). Probably the closest thing most companies had previously faced was mobile device programs. Now, any company that has a major portion of virtual team members is having to make this call.
There are pros and cons to each of these options.
Pros to BYOD
There are some good reasons to let employees use their own devices for remote work:
- It’s cheaper
- The devices are familiar to them
- You aren’t responsible for upkeep or fixing them if they break down
Cons to BYOD
There are some compelling reasons not to let employees bring their own devices for work:
- Security concerns
- Data storage and retrieval can be an issue
- If the device does break down, you may not be responsible but that employee may also not be able to work
Pros to COD
Supplying your own corporate-owned devices has a few benefits:
- Optimal control for access and security
- Subject to enforceable company rules for use
- Standardized systems and software
Cons to COD
Of course, there are some downsides to supplying all of the business technology for remote employees:
- Cost can be very high
- If the physical device is lost or compromised before being locked down, any info on the hardware could be susceptible to theft
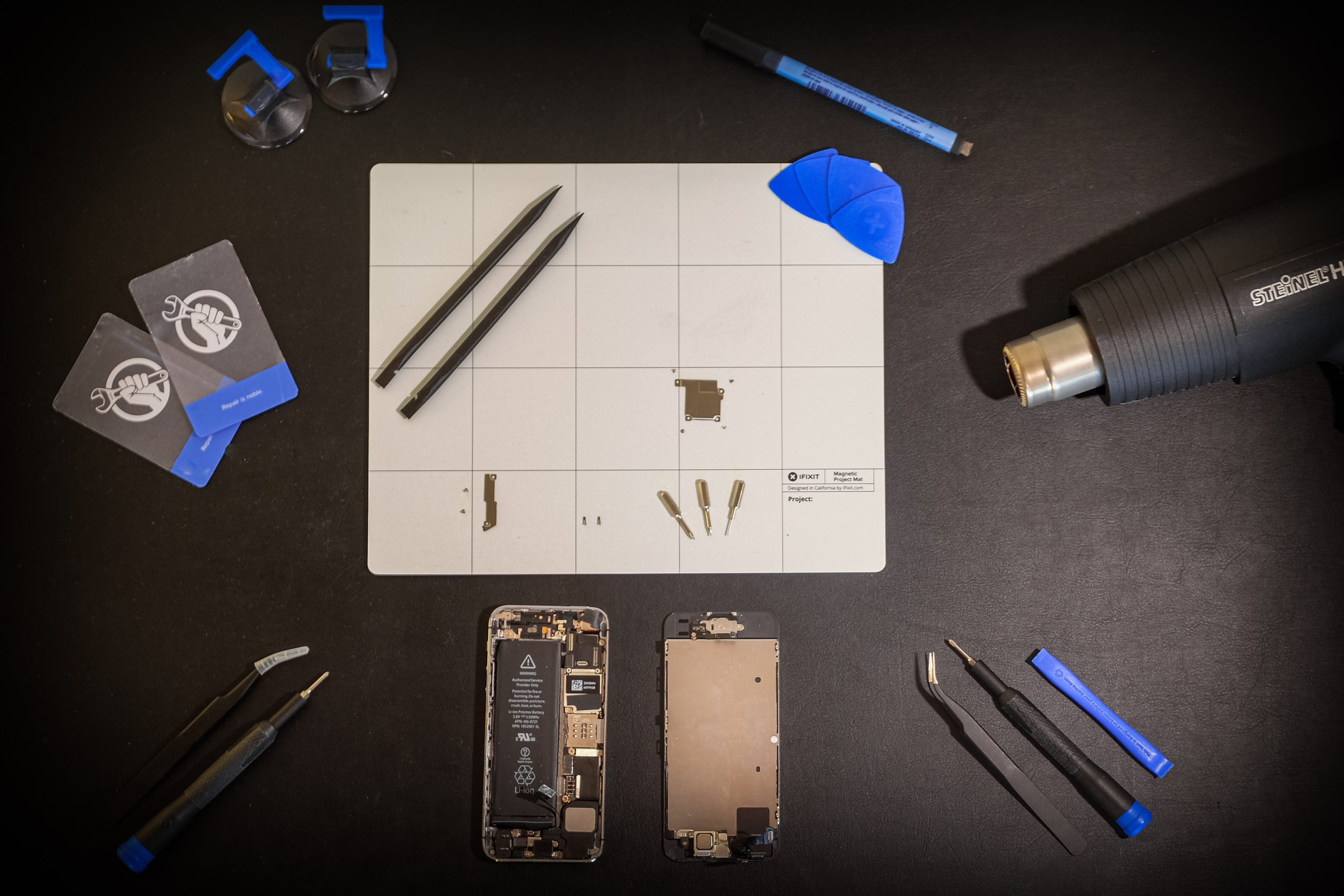
- Device management will be on you, or your IT team, and could be hard to do remotely
Device Lifecycle Management
That last point is definitely a sticking point for a lot of companies. The idea of activating their internal IT department to purchase, setup, deploy and then manage devices feels like an impossible ask. The good news is that this can also be an outsourced operation.
For instance, the team at Gadget Genie provides business-to-business IT services. Part of our IT services for businesses can include lifecycle device management. This means that we can alleviate some of the workload of setting up, distributing and then overseeing use of corporate-owned devices. It’s a great way to get all of the benefits with minimal risks or impossible workload. Contact us to learn more about this service.
Business Devices and Cybersecurity
Beyond cost, the second most crucial element of managing business technology has to do with cybersecurity. Since the summer of 2020, cyber fraud incidents increased by 45%, with as many as 4,000 attacks happening per day. Unbelievably, this number is expected to continue to go up. Bottom line? Cyber criminals realized the opportunity to attack employees working from home, and they weren’t shy about it.
Cyber attacks all the way up to government entities were common news this year. At some point, whether it’s a virus or a scam, work from home employees are going to face this threat. Businesses that deploy their own devices have a better chance of mitigating the risk.
BYOD cybersecurity risks include:
- Lost or stolen devices
- Cloud-based storage infiltration
- Corporate network security variations
- Exposed email
- Employee interactions
COD devices can solve some of these problems. Even when you do provide your own business technology to employees, it’s essential that all companies distribute and enforce protocol for cybersecurity. This includes training your staff on password hygiene, informing them about the latest attacks or possible scams, and installing the best antivirus software.
Additionally, how your business network is setup could leave you vulnerable to tracks. If you need an expert to audit your devices or your network, Gadget Genie has a team that can take a look. Just reach out.
Outsourced IT for Businesses
At the end of the day, whether you let employees BYOD or provide it all yourself, there is a tradeoff to be made. Virtual work is changing the way we think of departments and resource allocation. Many companies are looking into outsourced IT altogether. This is more possible than ever, due to technological capabilities and integrated systems. If you are interested in learning more about how outsourced IT work, lifecycle device management or even cybersecurity training could help your team, contact Gadget Genie. We can be your secret weapon for success.